Living, Learning and Connecting in Cyberspace
Together with KMCC (Kent & Medway Cyber Cluster Ltd) and KMCS3 (Kent & Medway Cyber Security Student Society), iCSS co-organised the 2023-24 CyberAnything Competition. The competition ran from late September 2023 and until early March 2024. KMCC joined the initiative as a co-organiser and a co-sponsor in late December 2023.
We increasingly rely upon digital, networked and smart technologies such as mobile devices and the internet to live our lives. Or we can say that we are living in the Internet of Everything (IoE), a cyber-physical world where so many hardware devices, software systems, physical things, systems and people are now interconnected. However, the cyber elements of our lives and how security, privacy and safety of such elements affect our lives are not always visible or overlooked, and sometimes intentionally concealed. They are often so entrenched in our way of being that we overlook our reliance upon them until they stop functioning, e.g., when a power cut, server downtime or an empty battery hits us.
This competition focused on anything that is cyber-related in our daily lives. All types of submissions were allowed and we received a wide range of submissions, including photos taken by participants, digital images (co-)generated by AI, videos, a puzzle booklet, posters, poems, essays, PowerPoint slides, and several physical objects such as a board game design, a decorated frame and a hand drawing.
Cash prizes
Submitted artefacts were eligible for the following prizes:
- 4 Best Overall Prizes (£80 Amazon e-voucher per prize, 1 across All Categories, 1 for UniKent students, 1 for UniKent staff, and 1 for Non-UniKent UK residents)
- 4 Most Creative Prizes (£80 Amazon e-voucher per prize, 1 for UniKent students, 1 for UniKent staff, 1 for UniKent alumni, and 1 for Non-UniKent UK residents)
- 8 Runner-Up Prizes (£20 Amazon e-voucher per prize, 4 for UniKent students, across all categories)
- 10 Director’s Picks (£20 Amazon e-voucher per prize, across all categories)
Best Overall Prize across All Categories
Fall-in-love victims and online catfishing, by Pornlapat Thopwongsri, MSc student, Kent Business School, University of Kent
The Internet, social media, and online dating applications make it easier for us to connect with other people, no matter where they are in the world. However, this simplicity also facilitates many malicious to access their targets more readily. This leads to issues like data fraud, financial fraud, and online harassment.
Scammers will pretend to be somebody who might be good-looking, well-educated, and trustworthy. may establish a fake profile using images and details taken from the internet. Deception by assuming a fake persona to exploit others. This behaviour is known as “Catfishing” *
I use AI “Video Gen” to help generate part of the patient.
UniKent Students: Best Overall and Most Creative Prizes
Best Overall
SecureCyber: Safeguarding our digital lives, by Nabeena Islam, UG student, School of Computing
I have created an infographic poster using Canva, which contains tips for cybersecurity.
Most Creative
Cyber themed puzzle Booklet, by Daniel Shorter, UG student, School of Computing
A cyber themed puzzle booklet. Designed for people to test theory knowledge in Cyber. Perfect addition to conference booklets for attendees to attempt in their free time etc.
UniKent Staff: Best Overall and Most Creative Prizes
Best Overall
Park Wood’s Tales of Connectivity, by Mickey Williams, Assistant IT Operations Engineer, IT Operations, University of Kent
A poem about the interconnectedness of our students living in Park Wood, both physically and electronically, with a growing sense of the dangers that being connected 24/7 is leading them to..
Most Creative
Anti mouse-ware, by Innes Hatton, IT Operations Engineer (Networks), IT Operations, University of Kent
Here we see one of our beloved support workers for the uni checking our systems and defences against the terrible viruses that plague the internet. This is our last paw of defence against the viruses that plague the internet.
UniKent Alumni: Most Creative Prize
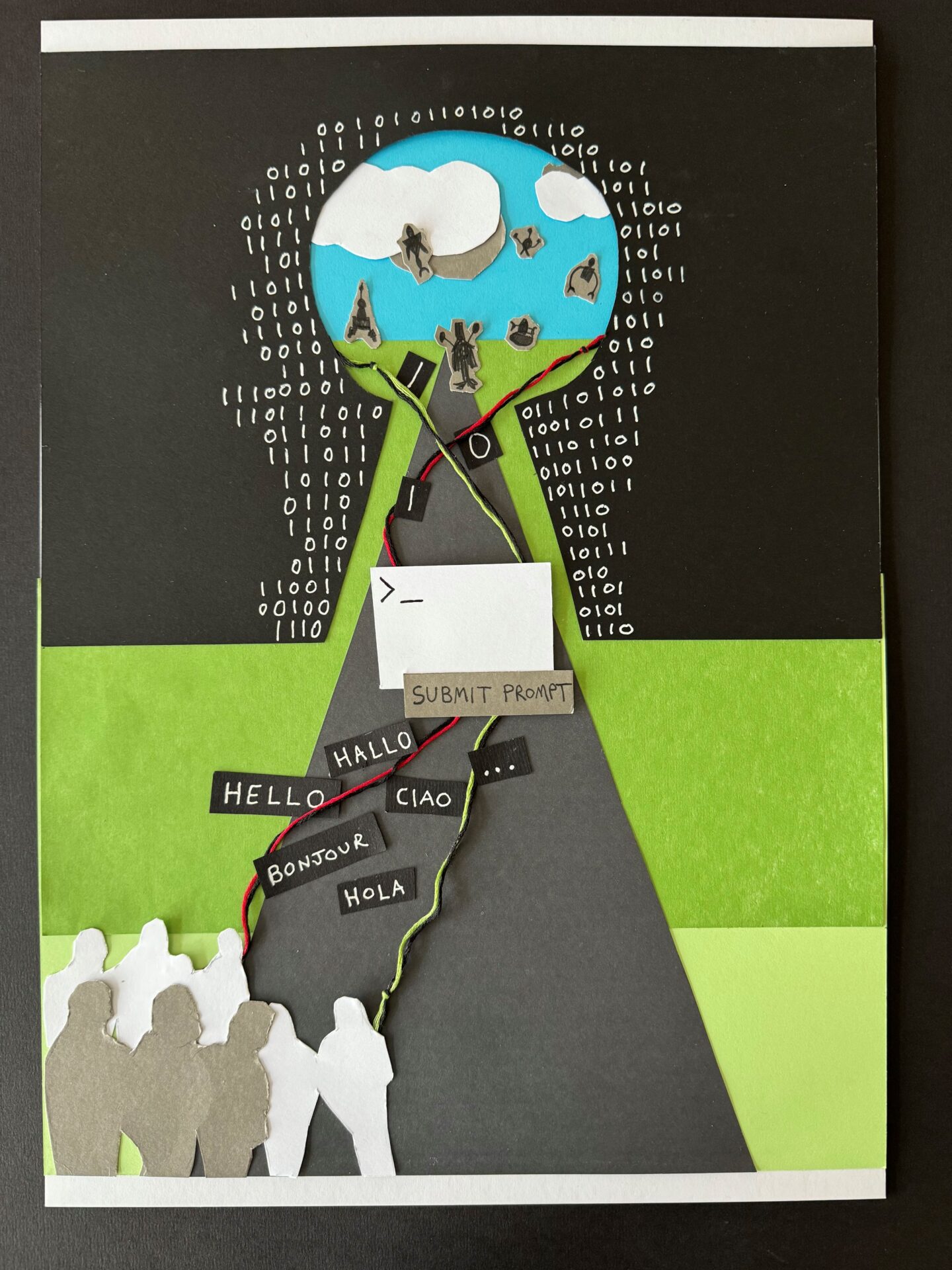
Submit Prompt, by Tom Neaves, Managing Security Consultant, Trustwave SpiderLabs & Former UG student (2002-05), Electronics Department, University of Kent
Capturing the literal road (or path) through the key hole and out into the horizon as we enter into the brave new world of AI. Humans on one side, AI powered robots on the other, connected via wires (to represent both the data and power source from humans), with the console flashing before us ready to receive a prompt. Human speech going in, binary coming out the other side to the machines. The key hole surrounded by binary again as we enter, almost as if it is spilling out.
Non-UniKent UK Residents: Best Overall and Most Creative Prizes
Best Overall
Phishing Attack, by Deep Deuja, MSc student, Kingston University
Tools used in making this animated video are
1. ChatGPT – To structure the storyline.
2. textmagic.com – To convert text to audio.
3. Renderforest.com – To facilitate animated characters and editing.
Most Creative
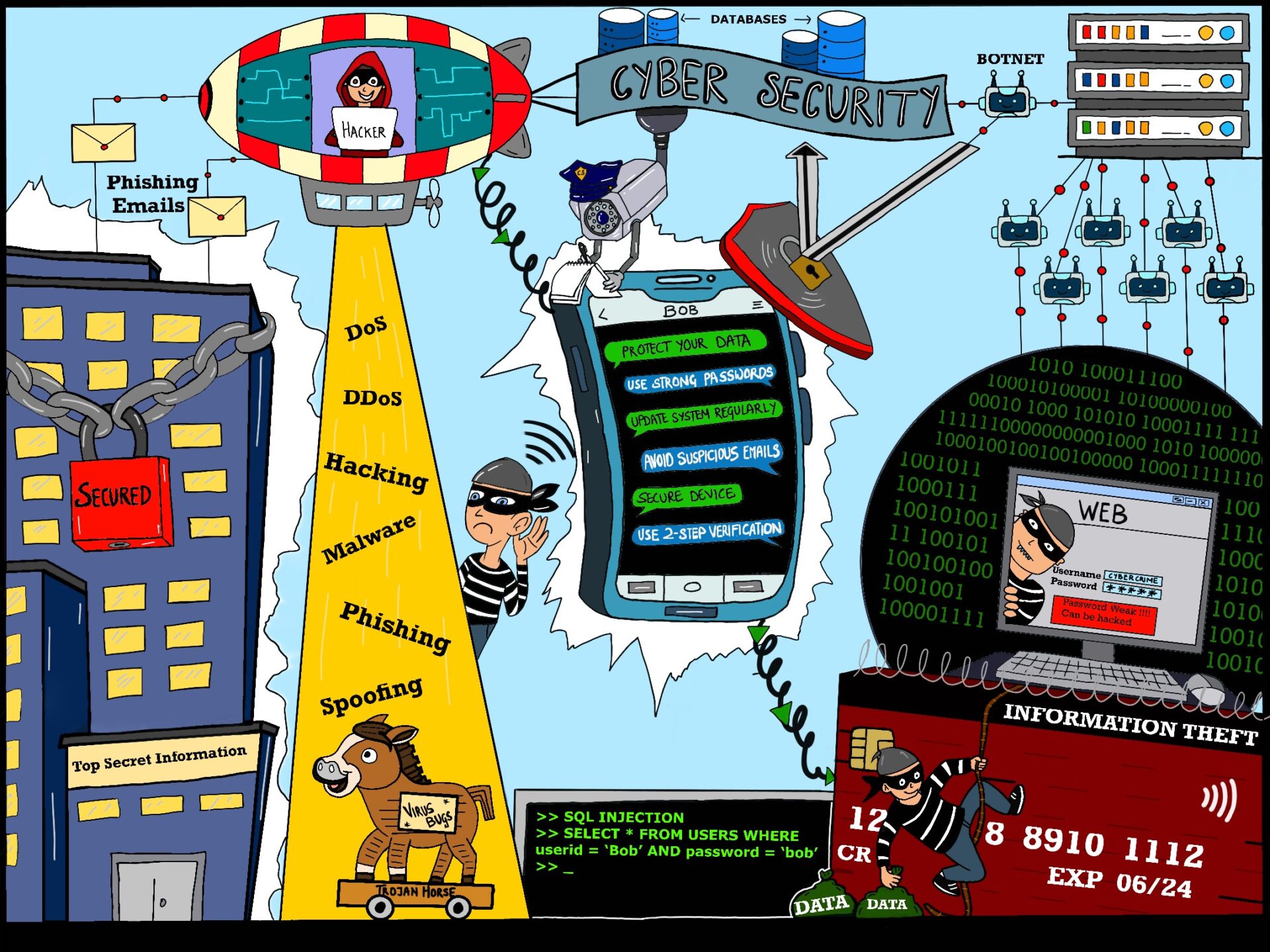
Cyber security poster, by Charlotte Elaine Rodricks, MSc student, Manchester Metropolitan University
The poster was made using sketchbook on an iPad. The poster depicts everyday cyber security attacks that could affect an individual and also gives some tips on how to avoid these attacks.
Runner-Up Prizes across All Categories
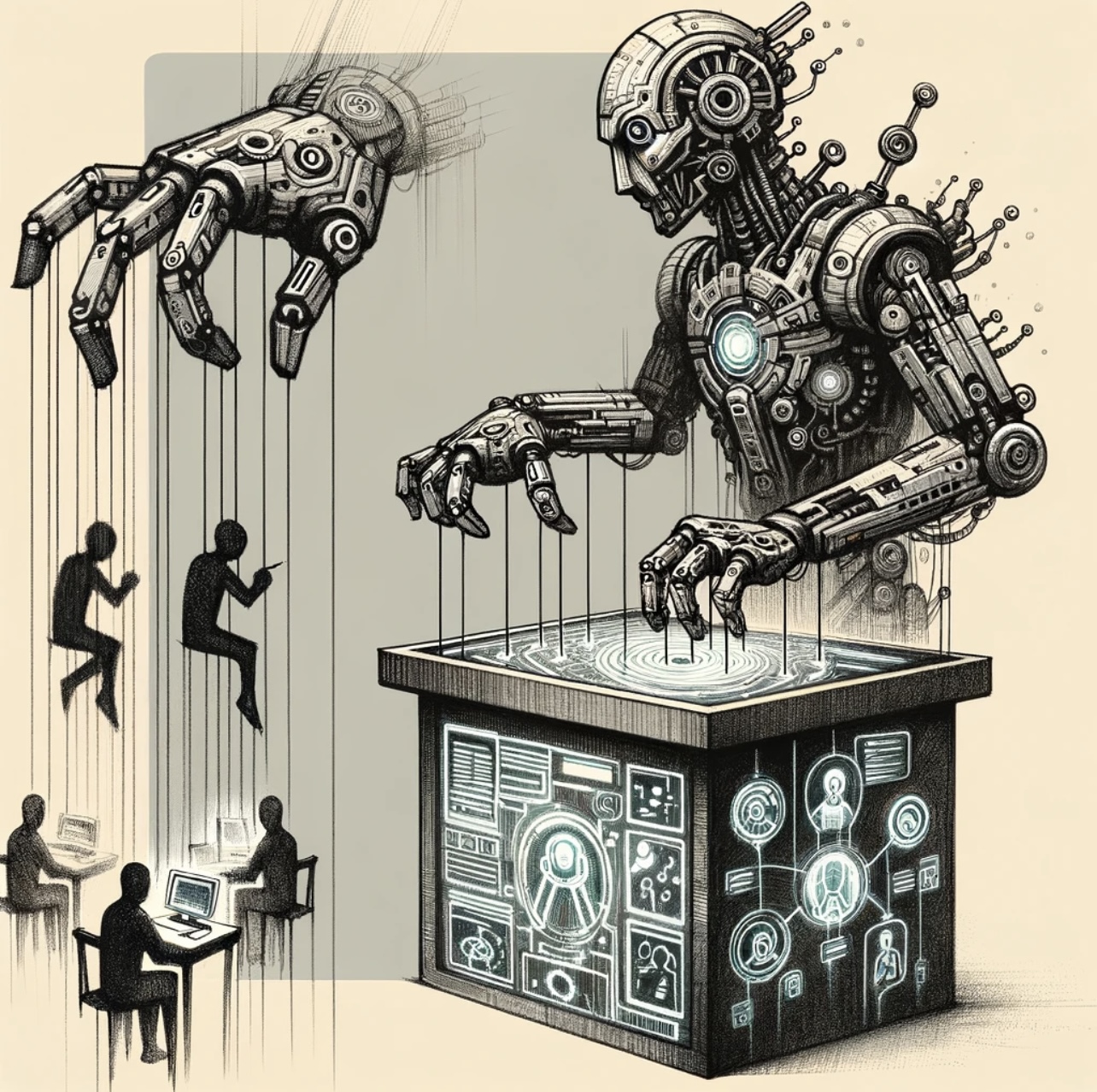
I am controlling u, by Yun Geng, PhD student, School of Arts, University of Kent
This is Yun Geng, PhD student in drama, I am currently doing the research about contemporary puppetry. And considering the relationship between cyber and human beings which makes me to rethink the puppeteer and puppet. Human in nowadays rely on the internet, however, we have to notice the security of it. Sometimes it can control us, so we need take care to use the internet. Then I use Chatgpt-4 to create the two images which include the elements of cyber puppet and controlling. As a PhD student in drama, my research currently focuses on contemporary puppetry. I noticed that the relationship between the digital realm and human beings such as puppeteer and puppet. Sometimes human is controlled by internet like a puppet. In today’s world, humans heavily rely on the internet; however, it’s crucial to be aware of its security aspects. The internet can sometimes control us, emphasizing the need for cautious engagement with digital platforms. To illustrate these concepts, I have employed ChatGPT-4 to create two images that encapsulate the themes of cybernetic puppetry and control
The prompt:
Design a cyberpunk-inspired puppet character tasked with educating individuals about online security while symbolizing control over humans through computers and phones via the internet.
Create an image based on a puppet with a cyberpunk aesthetic, designed to educate the public about cyber security or online safety. The puppet is transformed into a futuristic character but it like a master to control the human beings. To warn human beings to notice the security of the internet.
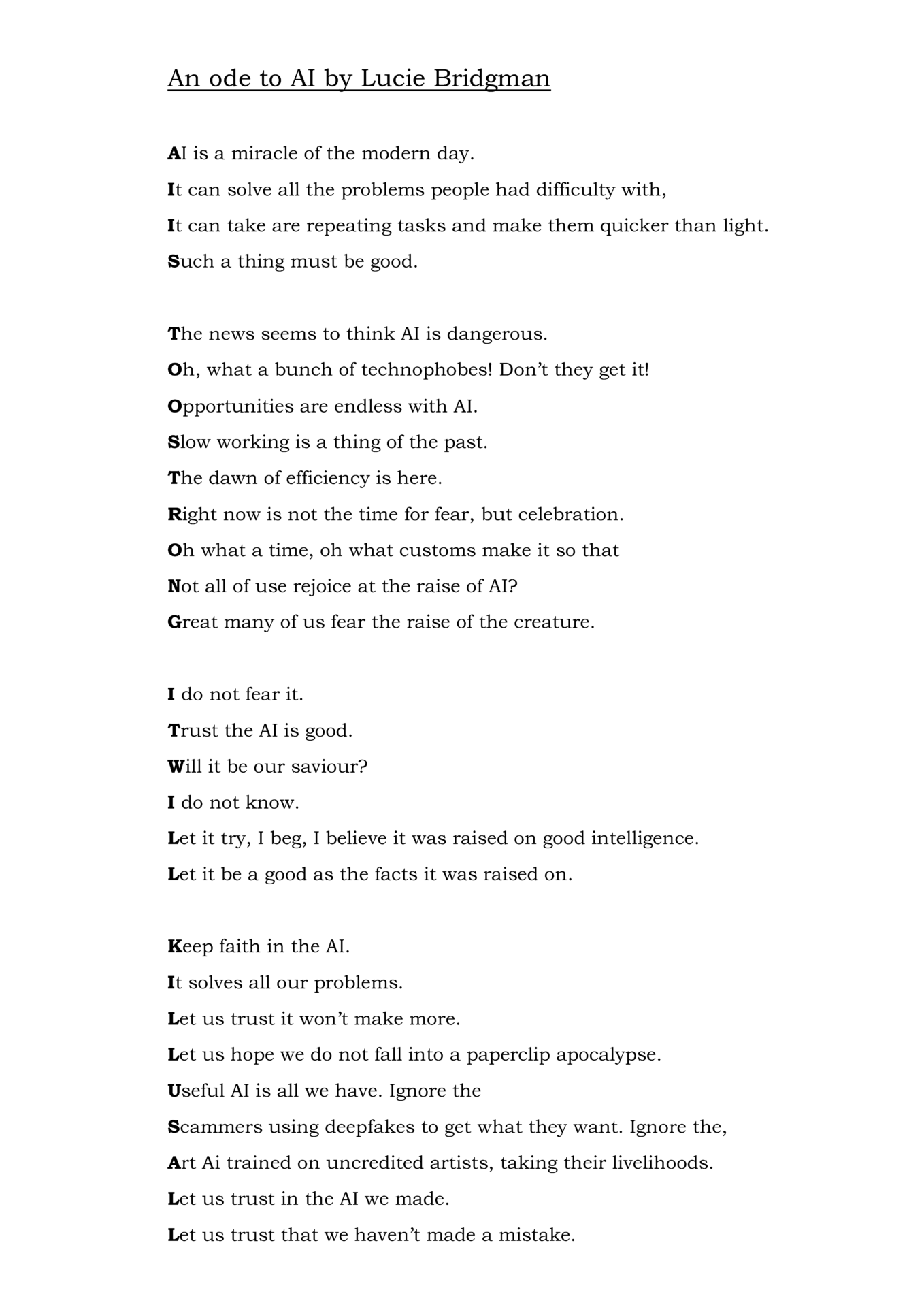
An ode to AI, by Lucie Bridgman, UG student, School of Classics, English and History, University of Kent
An acrostic poem about the good sides of AI and the bad sides of AI
CyberKitty, by Sreylin Strong, UG student, School of Computing, University of Kent
If your living space is safe, is your digital space safe too?
We wouldn’t want to keep our home doors unlocked, why would we do the same in our cyber home? Being part of the society (KMCS3) has greatly contributed to my self development and has taught me many things. But the most important lesson I’ve learnt was to be wary of our cyber space, especially as a woman. Our cyber space connects us to all of our loved ones and we want to protect them, us and you. So pay attention to your digital footprint and safeguard your privacy!
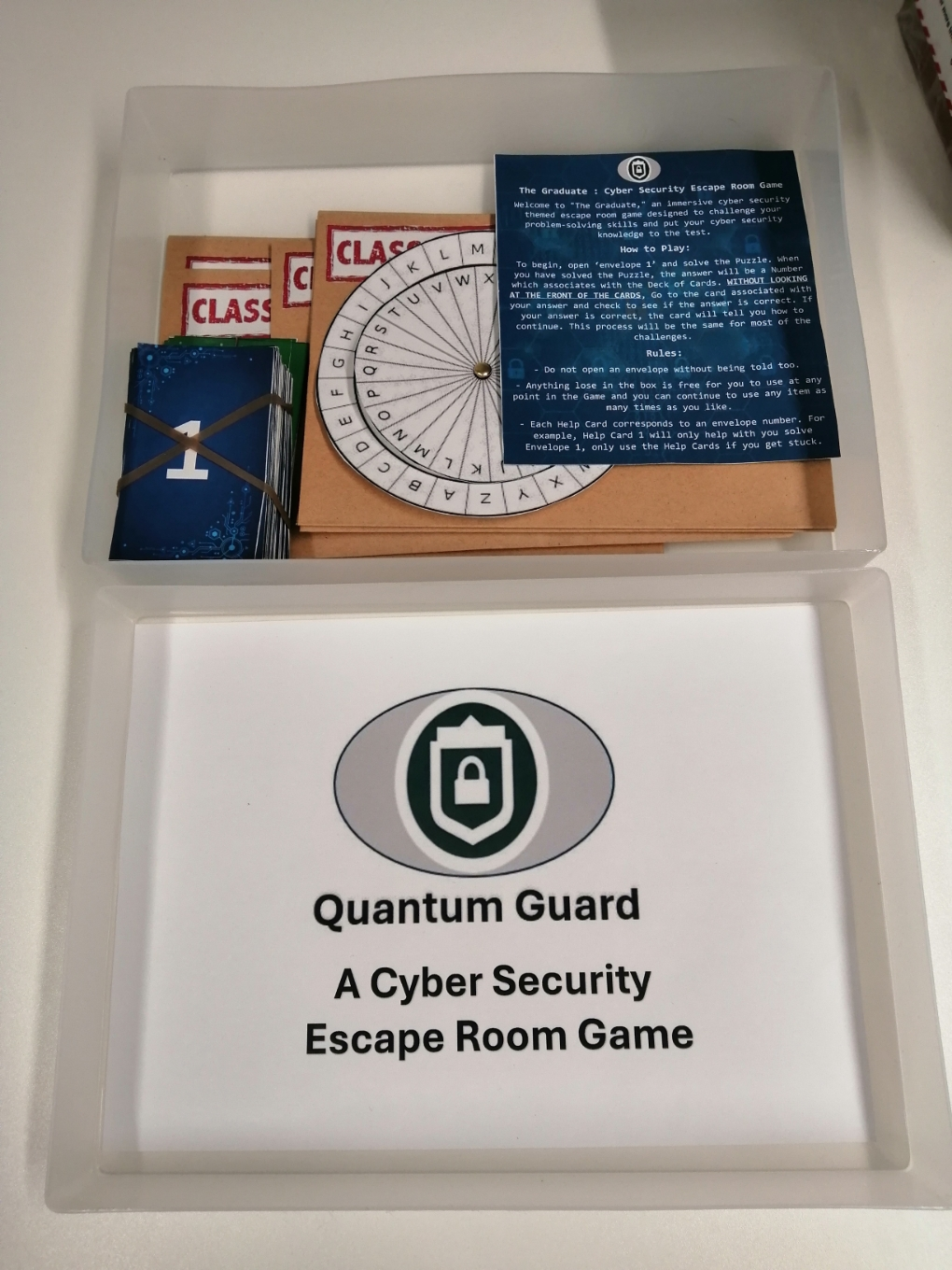
Quantum Guard | A Cyber Security Escape Room, by Jamie Champion & Caitlin Penmen, UG students, School of Computing, University of Kent
This is a Cyber Security themed escape room game teaching basic Cyber Security fundamentals, playable by anyone from any education background. AI was used to help create the storyline for the player (ChatGPT).
Mirrors of Deception: The Duality of Online Identities in the IoE Era, by Dr Athina Ioannou, Lecturer in Business Analytics, Surrey Business School, University of Surrey
In a highly interconnected world, else called as Internet of everything (IoE), the real identity of people can be easily concealed. Not everyone is who it seems in the online world. Through social media interactions, messaging apps and recently immersive environments, such as the metaverse, there are people, widely called in the public media as scammers, using fake identities to engage in various deceptive practices to exploit others; from phishing expeditions, impersonation of friends and colleagues, tech support scams and even romance scams, they usually aim for financial gain and other malicious purposes.
The image presented, generated by Chat-GPT 4 and DALLE, shows two people chatting online with each other. Yet, it poses an interesting question: which of the two is using a fake identity (i.e., scammer)? At first glance, the ‘darker’ figure seems to be the scammer. However, people can pretend to be anybody in the online world; a seemingly trustful woman pretending to be a man or a seemingly mysterious man pretending to be a woman? The two contrasting halves highlight the dual meaning of the image; each half representing a mirror to the potential duplicity that lurks beneath the surface.
The image aims to highlight the importance of being vigilant, alert and cautious in all our online interactions and verify identities when we can. Most importantly, as individuals we should strive to educate others around us, especially more vulnerable individuals, about potential scams that we may have seen before. Either in the workplace or in our personal life, safeguarding our privacy and security is crucial to our collective responsibility in an ever-evolving cyber landscape.
Prompt used:
Create an image that is divided in half: on the left-hand side a woman working on her laptop. On the right side, a man working on his laptop chatting with the woman. He is a scammer. The woman looks trustful while the man looks deceitful.
Your touch tells who you are, by Dr Pin Shen Teh, Senior Lecturer in Information Technology Development, Manchester Metropolitan University
Every individual possesses a distinctive signature when interacting with touchscreen devices. This signature covers various factors such as the speed of pressing, the size of fingertips, the pressure applied to the screen, and more. It holds the potential to enhance security by serving as an additional layer of authentication beyond traditional passwords or PIN numbers. This innovative technology is referred to as the Touch Dynamics Authentication System.
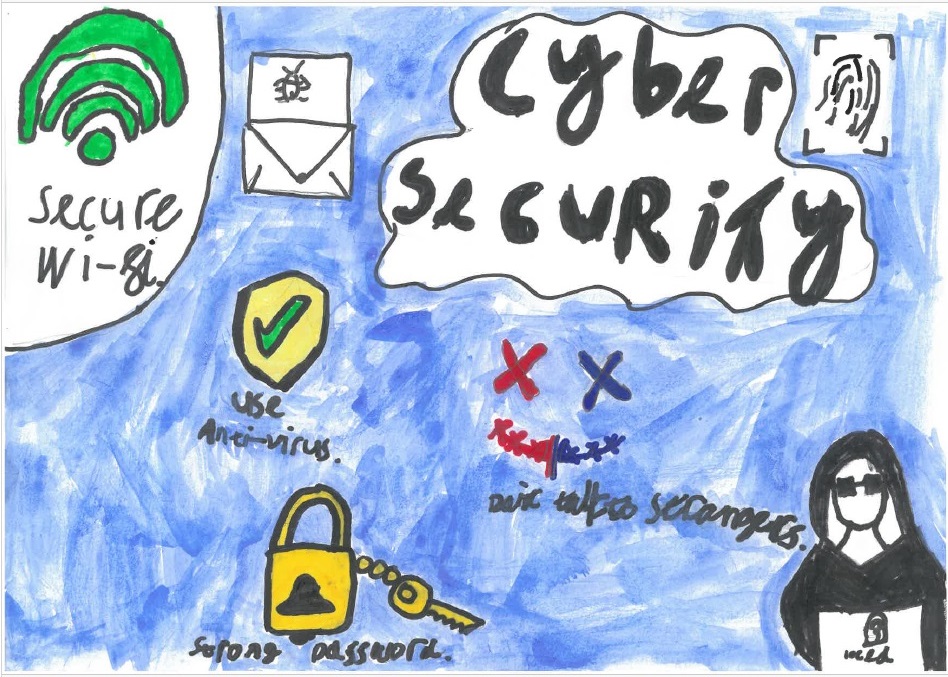
Cyber Security, by Henry Korra, pupil, Blean Primary School, Canterbury
Hand drawn and painted poster
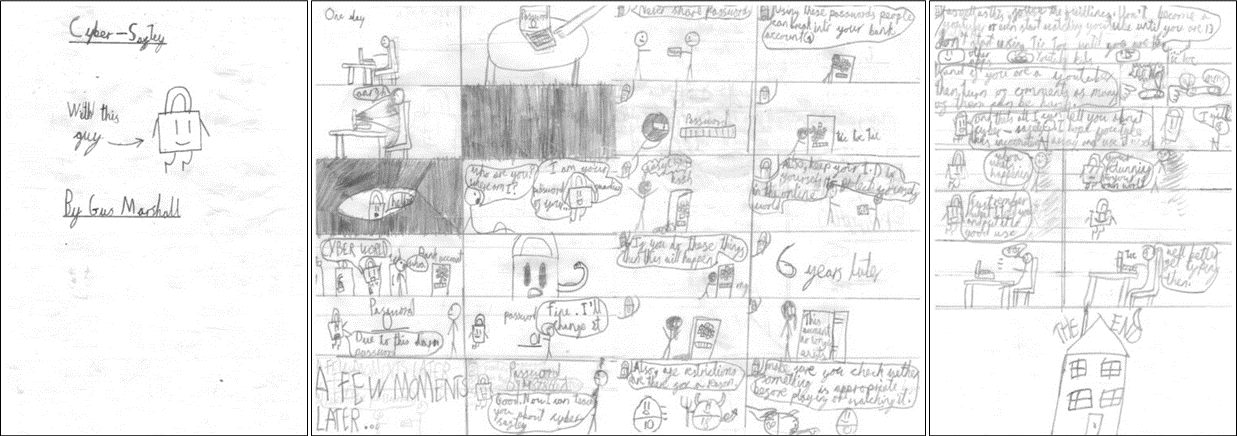
Cyber Safety Comic, by Gus Marshall, pupil, Blean Primary School, Canterbury
Comic strip booklet hand drawn
Director’s Picks across All Categories
How AI understand cyber security?, by Anguo Lu, PhD student, School of Arts, University of Kent
I first asked Chat GPT to describe an image about cyber security, and the answer I got was:
The image is a dynamic and visually striking representation of cybersecurity in the digital age. In the center, a large, vibrant shield glows with neon blue and green lights, symbolizing the protective barrier of cybersecurity measures. This shield is adorned with intricate patterns, resembling digital circuitry and binary code, highlighting the technological sophistication of cybersecurity defenses.
Surrounding the shield, a myriad of abstract digital elements, including streams of 1s and 0s, flow towards the shield, representing various cyber threats such as viruses, malware, and hacking attempts. These elements are rendered in contrasting reds and oranges, creating a clear visual dichotomy between protective measures and potential threats.
In the background, a faint silhouette of a globe signifies the global nature of cyber threats, with various nodes and connections illustrating the interconnectedness of modern networks and the internet. Overlapping the globe, faint outlines of padlocks and keys symbolize encryption and data protection methods.
In the foreground, a figure stands, perhaps a representation of a cybersecurity professional or a user. The figure is partially obscured, symbolizing anonymity and privacy, with their hands raised and interacting with a holographic interface that displays security metrics, firewall status, and real-time threat analysis.
The overall atmosphere of the image is one of vigilance and advanced technology, highlighting the ongoing battle between cyber defenses and threats. The color scheme, dominated by blues and greens against the warmer tones of the threats, reinforces the idea of cybersecurity as a cool, calculated, and essential field in the digital era.
Then, I used Stable Diffusion, an AI painting software to generate the images described by GPT.
I totally generate the same description for 25 times and got 25 images, and than put all of them together.
So in the end, we can see the image of cyber security in AI’s mind and also can see how different can the result be even though we use the same and detailed description words.
Cybersecurity Composition, by Emmanuel Fatimehin, UG student, School of Sport and Exercise Sciences, University of Kent
It’s a piano composition I made about cybersecurity. I don’t know much about cybersecurity but I just tried composing while thinking “does this feel cyber to me?”
Hiding Behind a Computer, by Margaret Thuesen, UG exchange student from the USA to the School of Arts, University of Kent
I took a photo and then used photoshop to change the colors around.
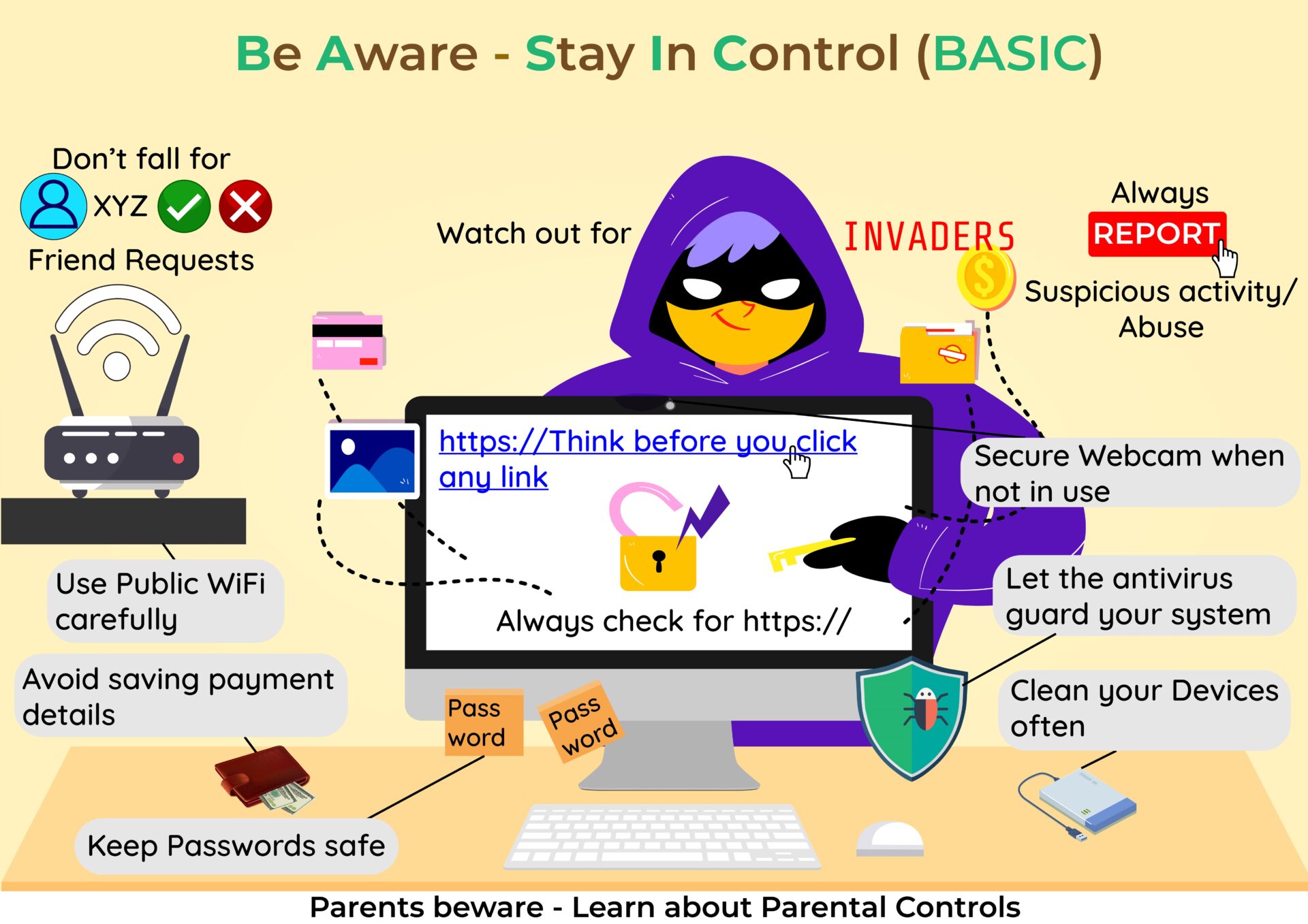
Be Aware – Stay In Control, by Harshavardhan Dhulipalla, MSc student, University of Nottingham
This is an awareness-raising poster regarding cyber security and cyber safety for lay people focused on the Basic protocols (Be Aware – Stay In Control) to avoid falling into the trap of cyber phishing, cyber problems, invaders, cyber thefts, data breaching, etc. These are common and simple methods such as:
1. Using public WIFI carefully and keeping our data restricted.
2. Avoid saving payment details on various shopping sites.
3. Storing passwords safe and not leaving them open.
4. Securing our webcams and maintaining our privacy.
5. Having strong and updated antivirus software.
6. Regularly formatting and cleaning our storage devices like hard disks and USB sticks.
7. Reporting suspicious activity, abuse, and even cyberbullying to the relevant authority.
8. Avoid clicking on unauthorized links and checking for ‘https://’ links.
9. Never accept friend requests from strangers.
This doesn’t mean that you can avoid hackers and invaders, there are many other pitfalls to fall into such traps, but such initiatives gives confidence to individuals to enter and explore cyberspace. Finally, every parent needs to be aware of parental controls and should be updated with the technology that is present in the competitive world.
Note: No Generative AI tools have been used in creating this poster.
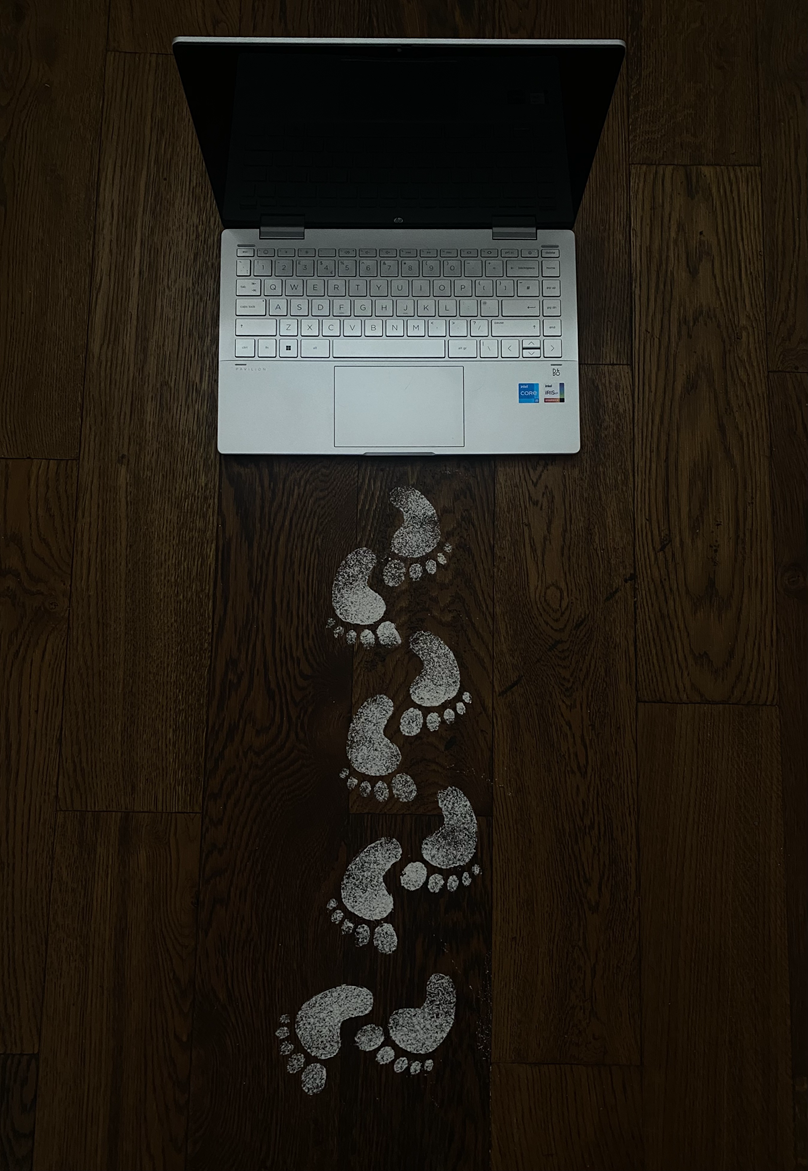
Traces of Risk, by Aimen Faisal, UG student, Manchester Metropolitan University
The trail of footprints leading away from the laptop in this image represents our digital footprints, the traces left behind from our online activities. Engaging in actions like clicking links, making online purchases, and sending emails carries the risk of our personal information being exposed to the vulnerable digital world, such exposure can have serious consequences if they fall into the wrong hands. The photograph serves as a strong reminder to always be aware of our digital footprints and ensure that we take the right steps to keep our online presence and personal details safe.
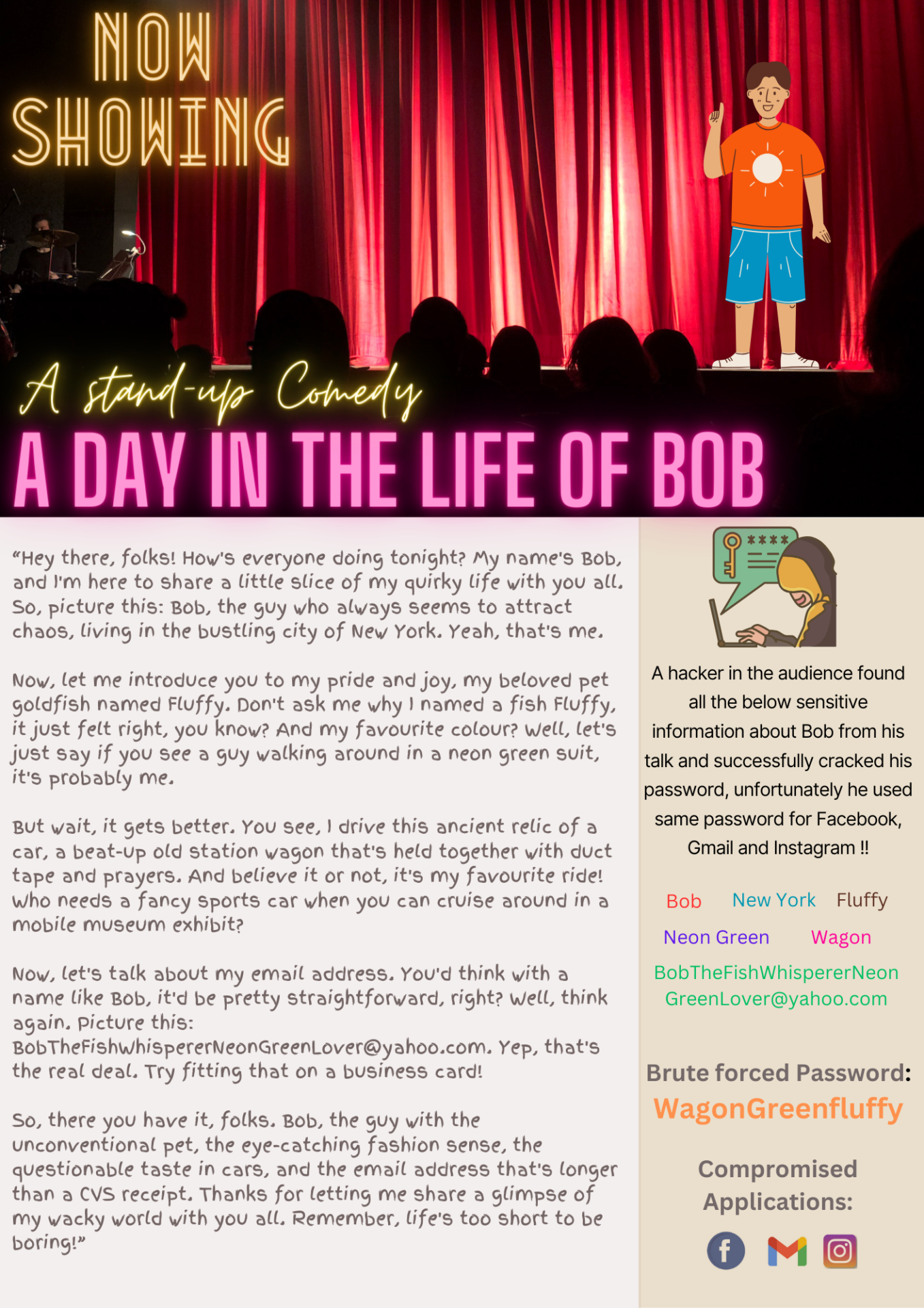
A DAY IN THE LIFE OF BOB – A stand-up Comedy, by Johnsey John, MSc student, University of East Anglia
The flyer is designed using Canva and the script used for the stand up comedy is generated using ChatGPT by giving the keywords such as name, place, pet name, favourite car and email ID.
Car Exploits, by Jack Christie, UG student, University of the West England
Infographic displaying various exploits that can be performed on modern cars along with graphical demonstrations of how these can be carried out. No use of AI tools were used, all work is original and uses legal licensing for images used. Made with PowerPoint 🙂
Deprive them of Power, by Andrew Mensah, UG student, School of Computing, University of Kent
Poster with a cyber criminal with a grey crown (signifying they haven’t got much power), with advice at the bottom.
Play the Game and be Cyber Aware, by Temesgen Kitaw Damenu, PhD student, School of Computing, University of Kent
A video which show cyber security games for children mainly found in literatures.
Copilot AI generated image used at the cover and end with the following query.
“Create a funny and educational picture for children about playing cyber security games with a title “Play the Game and be Cyber Aware!”
Canvas is used to create the video from pictures
Glitch, by Mailuo Shen, PhD student, School of Arts, University of Kent
Glitch art is the practice of using digital or analog errors for aesthetic purposes by either corrupting digital data or physically manipulating electronic devices. “Vulnerability” in cybersecurity seems subjectively to me associated with “glitching”. Today, in an age of digital technology, could a “vulnerability” affect the reality? By using “Glich” as a kind of figurative “vulnerability”, hopefully in the future, we can create an interactive installation or game, through which the audience can “attack” or “fill” the “vulnerability” in cyberspace(VR probably), and in this way, to help especially young people to notice and protect the cybersecurity of their own.